Can Mac get ransomware? It’s the question you secretly dread to know the answer to. The answer remains a mystery, and your guess is as good as mine. Despite Apple's extensive efforts to safeguard its ecosystem, the risk of ransomware attacks on Macs still looms.
Ransomware stands as an ever-constant threat to global cybersecurity, impacting individuals and organizations alike. Shockingly, in the latter half of 2022, statistics revealedthat ransomware attacks surged from over 102 million cases to nearly 155 million worldwide.
If you're a Mac user, you're likely pondering your vulnerability to such threats and seeking guidance on strengthening your defenses in the event of a ransomware attack. This article provides all you need to detect, avoid, and remove ransomware from your Mac.
Read on!
What Is Mac Ransomware
Ransomware remains one of the most potent cyber threats worldwide, with the potential to significantly disrupt businessoperations and cause financial damage. It's a type of malicious software that blocks access to your most important files until you pay moneyto unblock them.
A Mac ransomware is simply ransomware that targets Apple desktops and laptops. Even though not as prevalent as the ransomware variants attacking Windows computers, Mac ransomware is still every bit as horrible.
Just like attacks on other devices, the motivation for a Mac ransomware attack is still financial gain. Sometimes, the attackers may change their objectives and only aim to disrupt operations that cause downtime and reputational harm.
Other attacks may be deployed alongside ransomware, such asdistributed denial of service (DDoS), to create additional pressure on the victim. Here is a deep look into how a ransomware attack can be launched on your Mac:
Infection And Distribution
Attackers manage to get ransomware to your Mac system through various means. One common method is through phishing emails containing malicious links or attachments. If you click on this email, the ransomware will be downloaded, waiting for its execution.
Another method involves exploiting services like Remote Desktop Protocol (RDP). Attackers who acquire or guess your computer login credentials can use them to access your device, where they download and run the ransomware.
Data Encryption
This is the next crucial stage where the attackers execute the ransomware attack. Once they manage to get the ransomware inside, they’ll ensure it begins encrypting files. It accomplishes this by accessing files and encoding them using an attacker-controlled key.
All the original files on your Mac could be replaced with encrypted versions. Remember that ransomware often selects files cautiously to maintain system stability. Some variants even delete backup and shadow copies of files to hamper recovery without the decryption key.
Ransom Demand
The last and most crucial step involves demanding payment for the encrypted files. The methods vary among ransomware variants. One common method is for your Mac’s background to change to a ransom note.
You’ll also learn of a ransomware attack if the text files containing the ransom note appear in each encrypted directory. Typically, these notes demand payment in exchange for file access.
If you pay the ransom, the attacker provides either the private key used for encryption or the symmetric encryption key itself.
How To Protect Your Mac From Ransomware
You can make your Mac more secure and safe from ransomware attacks by adhering to the following tips. These measures protect your device from malware and will also serve you in general, ensuring you don't fall victim to common cyber-attacks.
Be Cautious With Email Attachments
Email remains a prime gateway for ransomware to infiltrate your Mac. If you get an email attachment from an unfamiliar or suspicious source, refrain from opening it. Stay vigilant for imposters posing as people you know, attempting to lure you into opening infected files.
Employ Malware Protection
Conducting routine antivirus scans is essential for identifying and removing malware. However, traditional scans may be inadequate when ransomware locks you out or encrypts your data. To combat this, opt for anantivirus software for Macwith real-time protection.
Such tools actively monitor for malware, preventing it from operating and making unwelcome alterations to your Mac.
Beware Of Phishing Emails
Criminals prize your data, and phishing scams aim to steal it by deceiving you into revealing sensitive information. These scams may employ fake login pages, quizzes, or other tactics, but the outcome is consistent: hackers gain access to your accounts and potentially introduce ransomware. Educate yourself about common phishing attacks to stay protected.
Implement Two-Factor Authentication (2FA)
Two-factor authentication (2FA)is a robust defense against unauthorized access. Even if attackers obtain your username and password, they'll need your authentication method, typically your phone.
2FA generates one-time passwords sent to your phone at brief intervals, making it challenging for criminals to breach your accounts and unleash ransomware on your Mac.
Avoid Untrustworthy Websites
Visiting dubious websites can inadvertently introduce malware, including Mac ransomware. Malicious downloads or rogue adscan also lead to infection. While this risk exists on any site, it's more prevalent on disreputable ones that have fallen under the control of hackers.
Avoid adult content, piracy sites, and unfamiliar sites, and resist clicking on pop-ups.
Keep Your macOS Updated
Hackers continuously seek software vulnerabilities to exploit. Responsible developers release updates and patches to plug these gaps. Regularly installing updates for your apps and macOS is crucial. Neglecting updates leaves your Mac susceptible to malware, including ransomware.
Remember that macOS houses numerous features that protect your Mac and data from malicious software. For instance, you can change your privacy and security settings to specify the sources of software installed on your Mac.
This helps you reduce this risk by using software only from reliable sources. Here’s how todo it:
- Go to Apple menu
- Click on System Preferences
- Click on Security & Privacy
Go to General
Here, you can choose the sources from which you'll allow software to be installed.
How To Remove Ransomware From Your Mac
So, let's assume you get caught out, and attackers manage to infiltrate your Mac with ransomware. The next steps you take are crucial to recovering your lost information and protecting your device from further damage.
If you've decided against handing over a ransom to cybercriminals, here are some alternatives to consider:
Check Activity Monitor
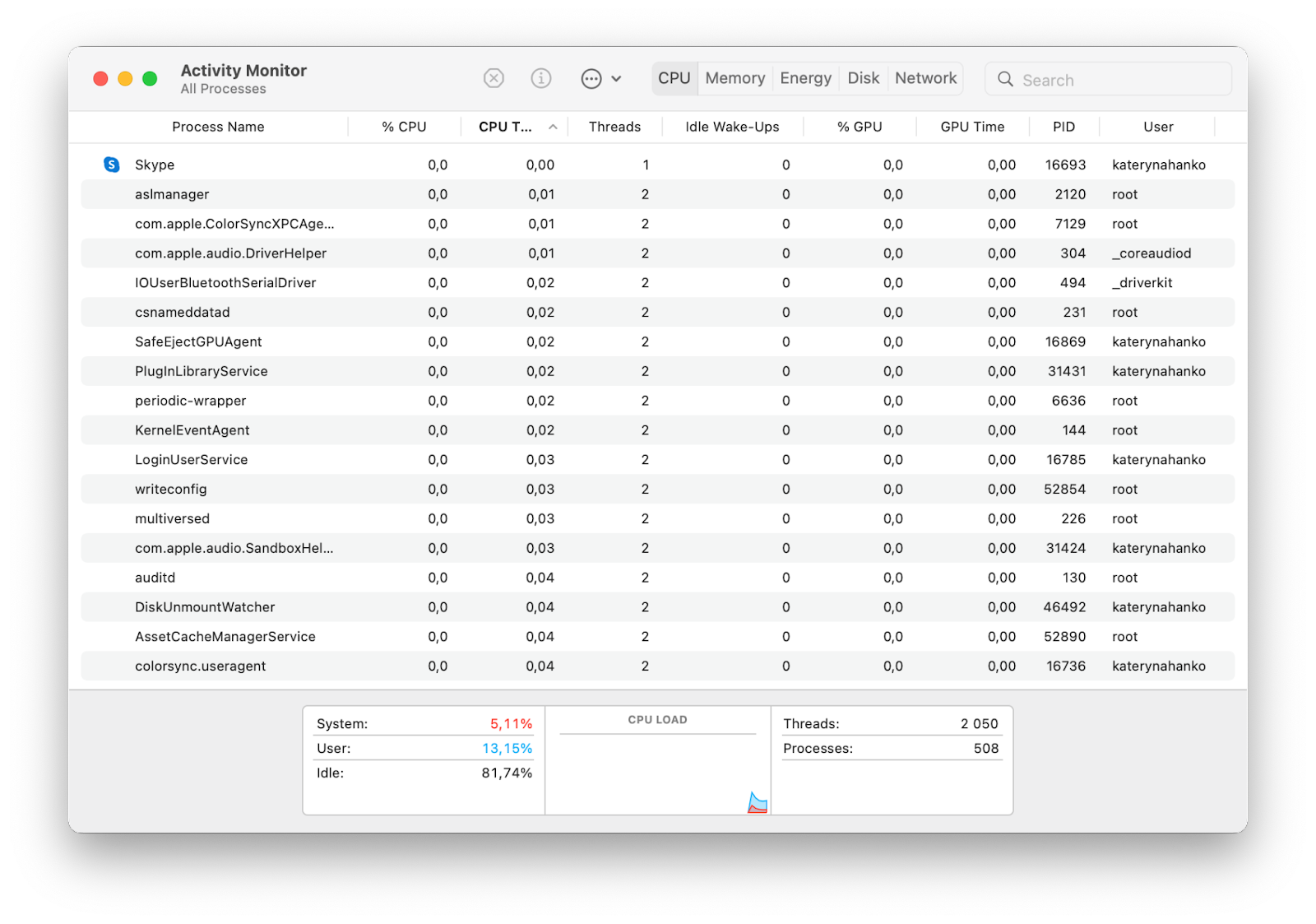
Examine the Activity Monitor, a native macOS tool that reveals running processes, including background operations. It’s one of the common ways to know if your Mac has a virus. If your Mac exhibits unusual behavior, a potential malware infection could be the culprit.
Keep an eye out for any processes consuming excessive CPU cycles or RAM, as these may indicate malware presence. Here is a simple guide to check Activity Monitor for macOS malware:
- Open Activity Monitor from Applications
- Click the CPU tab, then sort processes by highest CPU usage (% CPU)
- Look for unfamiliar processes with high resource consumption.
Disconnect From The Internet
Isolation is key to preventing further data transfer to malicious servers and halting the malware's spread. If you suspect an infection, stay offline as much as possible. Only reconnect after ransomware removal is confirmed or when necessary for downloading a removal tool.
Here’s how to disable Wi-Fi on a Mac:
- Go to System Preferences and click Network
- Select Wi-Fi
- Click Turn Wi-Fi Off.
Run A Virus Scan
If your Mac is operational and you can run apps, utilize your security software to perform a malware scan. While it may detect and remove the ransomware, success isn't guaranteed. Criminals often disable or encrypt security apps.
Remember that removing the malware won't automatically decrypt your data. However, installing and running security software that offers protection against ransomware and viruses is a crucial first step toward securing your data.
Wipe Your Mac
Sometimes, your primary concern after a ransomware attack is regaining access to your Mac and data. In this case, recovery is less of a priority. The viable option is to perform a factory reset and remove everything from your device.
This process wipes your system drive and reinstalls macOS, eliminating Mac ransomware and other malware. As an extra precaution, ensure any connected external or secondary drives are cleared to prevent reinfection.
Restore From A Backup
Backups serve as a strong defense against ransomware. You can restore encrypted data using Apple Time Machine or third-party backup solutions. Be cautious, as criminals may infect and encrypt your backups.
Also, avoid connecting external drives to your Mac while it's infected to prevent further spread. One backup option to consider should be cloud storage - your cloud-stored files are often safe from ransomware.
But before connecting to your cloud accounts, ensure your Mac is ransomware-free, either by conducting a virus scan or factory resetting.
Final Thoughts
Protecting your Mac against ransomware and successfully eliminating it without yielding to hackers is indeed achievable. By implementing proactive measures and understanding how to combat ransomware, you can ensure that your valuable data remains beyond the reach of cybercriminals.
Remember, your Mac's security is ultimately in your hands, and with the right knowledge and tools, you're one step ahead of cybercriminals. So, empower yourself, protect your Mac, and rest assured that you need not part with a single cent to these malicious actors.